Bug fix regarding tiling images on a single display in multidisplay setups.
Year: 2012
-
Rat as Jellyfish

Janna Narwoth, advised by Kit Parker at Harvard, created a jellyfish mimic from the cardiac muscle cells of a rat. (Video after the jump.) Copying the structure of Moon Jellies, the cardiac muscle cells were grown so that they were aligned into ring shape on a sheet of polydimethylsiloxane. When electricity is applied, the muscle cells contract, deforming the ring into a bell shape. When the electricity us removed, the cells relax, and the natural elastic properties of the substrate reflatten the disk. Examining the fluid dynamics, the mock jelly not only propels itself, but also creates a counter vortex that drives particles up and into the center of the bell, just like real jellyfish. The researchers hope to apply this technology as a tested for examining the effectiveness of certain cardiac drugs.
-
Ron Jeremy’s Phone Book
Categories: tech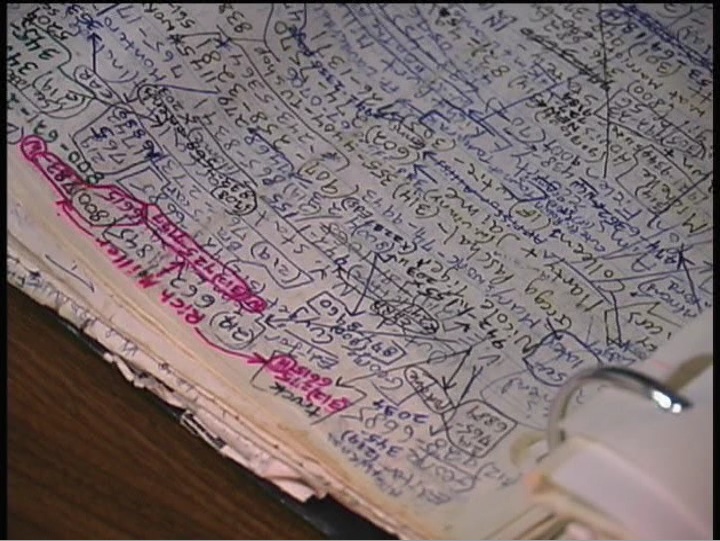
I just finished watching Porn Star: The Legend of Ron Jeremy. It’s a perfectly fine documentary, but didn’t really tell me anything I didn’t already know. Yes, Ron Jeremy is perhaps the most famous porn star. Yes, he doesn’t look like a porn star. Yes, he wants to be a mainstream actor. Yes, he’s beloved. All of this has been covered before. The one thing I did find interesting was Ron Jeremy’s “phone book.”
He carries with him a binder of loose leaf paper that is haphazardly covered with names and phone numbers. It’s organized by location of the person recorded. In the film, he reveals that some of the pages are dedicated to:
- New York City
- Los Angeles
- Other US locations
- International
- Radio Stations
Now a guy keeping all of his phone numbers scribbled on pages in a binder isn’t that interesting, but what I did find interesting was that he linked various people in the together into a social graph. Different numbers are annotated with labeled arrows form one number to another. He uses this information to place the name and number in context. Now that is something I haven’t really seen before. Yes, Apple AddressBook.app &endash; and presumably others &endash; has the ability to to add fields like “spouse”, “friend”, and “child”, but these aren’t links, just additional text fields. It seems like allowing a user to to crawl their personal social graph might be a useful feature for address books. Even if it isn’t used often, it doesn’t necessarily add a lot of UI overhead.
-
Koi Pond 2
Categories: animation / interactive / film
On advice of a coworker, I downloaded “Koi Pond” to my iPhone. Gloria said that it was popular with her three year old daughter.
The “game” is just what it says &endash; it’s a koi pond. There is what’re that you can interact with (the main attraction for her daughter and Maximilian), fish to watch swim about, lily pads to place. You can spend real money to buy more fish and ponds, but there really isn’t a point to do that. There are no goals. No achievements. Just you and the pond.
Contrast this with “Koi Pond 2” where I can’t open it without facing a pond full of dead fish because I haven’t logged in and cleaned a fish filter. All the advantages of having a koi pond: watching the fish, the sense of calm, are gone and replaced with the grind of maintaining a pond, and all the guilt and the daily grind of a tamagotchi. All the traps / trappings of contemporary casual gaming are there: daily play rewards, a store that takes real money, unlockables. Far from feeling rejuvenated, I feel like my soul has been sucked dry every time I open it.
-
Party Hard Bahrain!
Categories: other
Andrew W.K. of hitting himself in the face with a brick until he bleeds fame, has – according to his website – been invited as a cultural ambassador to Bahrain, “to promote partying and positive power.”
Awesome.
UPDATE Nov 26 2012 15:23 PST
Alas, Salon is reporting that the State Department has uninvited AWK.Bummer.
-
A Tool to Deceive and Slaughter

Caleb Larsen‘s “A Tool to Deceive and Slaughter,” sells itself on eBay every week. Every ten minutes, the microcontroller inside the the acrylic box wakes up and checks connects to a server that then checks eBay for an active auction. If none exists, then the server creates one. Each owner agrees to keep the work connected to the Internet at all times, and to set the starting price at “market expectations.”
Current price: $7500.Larsen says his work represents the temporary nature of ownership, and draws form Robert Morris’s “Box With the Sound of Its Own Making”, a wooden box that contains an audio recording of the carpentry work done to construct the box, and Jean Baudrillard’s ideas on art auctions
via
WiREDWired UK -
Pwnie Express
Categories: techTags: security
Pwnie Express, a company that apparently receives DARPA funding, develops clandestine network sniffers. Disguised as innocuous power strips or transformers, these boxes hide Ubuntu powered computers that contain packet sniffers and keyboard loggers with cellular network connections.
This isn’t a particularly new idea. I seem to remember a computer disguised as a UPS back in the late 90s or early aughts. There was also talk of using gum stick computer powered over ethernet as an inline network sniffer, although I wonder if it would have really worked back then. Still, these types of things always fascinate me, even if they seem relatively straight forward. It’s spy technology! I imagine sneaking into office buildings and secretly installing these either Mission: Impossible &endash; or more likely &endash; Sneakers style (i.e. in plain sight), and then retiring to a delivery van filled with electronic gear and retrieving whatever secrets I was looking for.
Needless to say, I have no use for these thing in real life.
via zdnet
-
Mobile Phone Keyboard Logger
Categories: techTags: arunabhverma, haochen, henrycarter, keyboardloggers, liangcai, mobiles, patricktraynor, philipmarquardt, security
Two related links, both involving using your phone to shoulder surf your passwords. Both attacks take advantage of the fact that smart phones with accurate accelerometers are now ubiquitous. By monitoring the the vibrations of the phone, the attacks inver what keys were pressed on a keyboard. Both of these a much more proof of concept, than actual sophisticated attacks, but they are interesting none the less.
At HOTSEC 11, Liang Cai and Hao Chen of UC Davis were able infer which key was pressed on an onscreen keyboard with 70% accuracy. By measuring how far phone was torqued around both the X and Y axises, the the location of where force was applied, and thus which key was pressed can be inferred. Cai and Chen made the task a bit easier for them. They held the phone in landscape mode, which spread the keys out more, thus causing a larger distribution of torques that could be measured. That’s not necessarily a problem since many people type in landscape mode. The bigger simplification was that they only looked at a touches on the dialing pad. A more interesting paper would have looked at attacking the alphabetical keyboard instead. I understand why they didn’t. The experiment was to find out if someone could use the accelerometers to read key presses at a high enough accuracy. Looking at their confusion matrix, I would think that determining alphabetical keyboard presses would need to be a two step solution. First, you’d get a distribution of what key was pressed. You’d then combine these presses with a Markov Chain language model to determine what the actual keyboard press was. “it was the durst of timez” becomes bit more Dickensian, a little less crappy rap-rock, and a lot less monkey.
Of course, sniffing the phone’s keyboard is one thing, figuring out what someone is typing on their laptop or desktop is something else, but that’s exactly what
Philip Marquardt and others at Georgia Tech did. In their work published at CCS 2011, they describe a technique where a phone placed next to keyboard read key presses via vibrations on the table at 80% accuracy. Unlike the method above, this team used a dictionary to increase the decoding accuracy. Their method feels the vibrations through the table and then attempts to categorize the key being on the left or right side of the keyboard (assuming the phone is placed to the left of the keyboard). Pairs of key presses are read, the distance between the first and second key of each pair is categorized as being either “near” or “far”. These triple are then passed through the dictionary in order to figure out what is the most likely English word typed. Left-right and near-far categorization is done using a neural net. -
Discouraging Voters
Tags: politicsEmily Bazelon at Slate has written a short essay lamenting the fact that access to polls has become a partisan issue. In other words, the Republican Party is transparently engaging in widespread voter suppression.
I will never understand why someone would not want to make it as easy as possible to let people vote. There’s something wrong if you’re in politics and you depend on an unengaged electorate.
